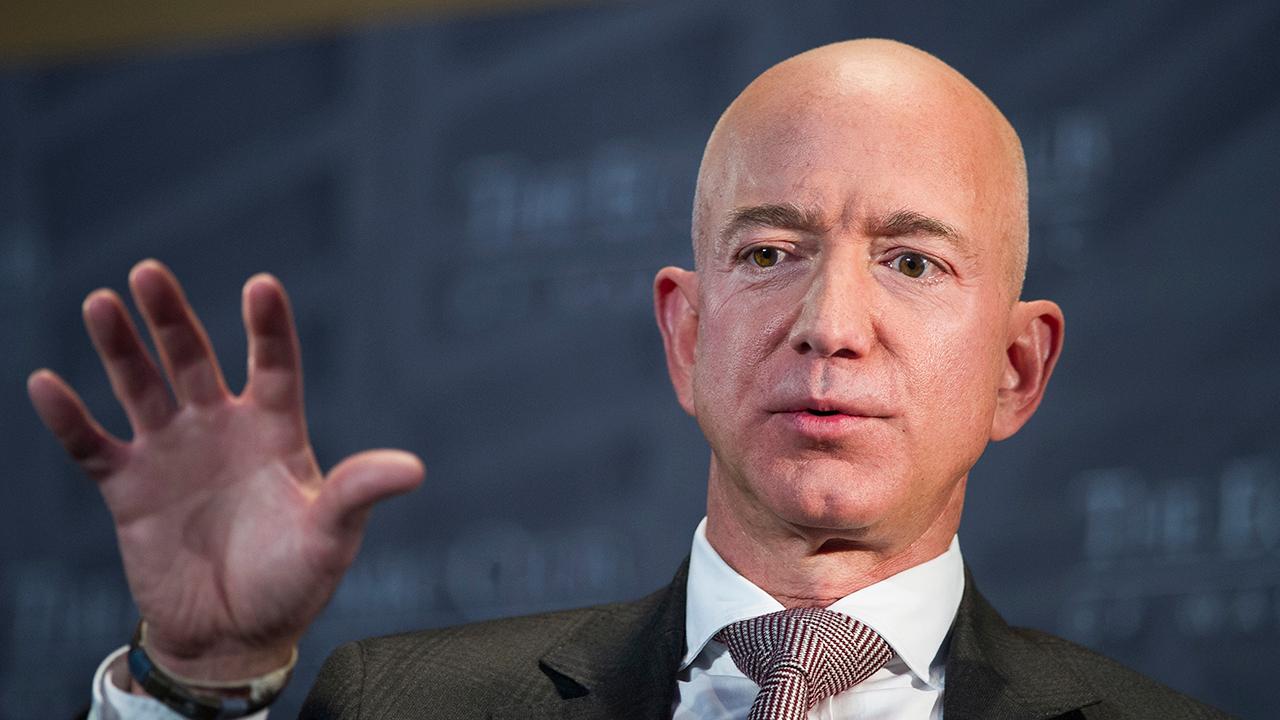
Jeff Bezos iPhone hacking: How to protect your phone from cyber hackers
60% of Americans say they or a close family member has been a victim or a phishing attack.
Some people are wondering how hackers tricked the founder of the most valuable brand in the world into watching a video on his iPhone that contained malware.
Two U.N. experts called for an investigation by the U.S. into information they received suggesting Amazon founder Jeff Bezos opened a malware-containing video message on the Facebook-owned messenger WhatsApp that appeared to come from Saudi Crown Prince Mohammad Bin Salman's personal account in 2018.
Check Point, a software company, has conducted extensive research on WhatsApp since 2018 and exposed vulnerabilities in the app that led to scams like this one involving Bezos, as well as updates in the app that have helped fix those vulnerabilities.
"Instant messaging and social media – as we’ve seen in the last three years – these are the mains target today from a phishing attack perspective," Oded Vanunu, Check Point head of product vulnerabilities research, told FOX Business. "We are talking about billions of people using these apps; [they] are used on all types of devices all over the world."

The fiancee of murdered Saudi Arabian journalist Jamal Khashoggi, Hatice Cengiz (fourth from left) and Amazon CEO Jeff Bezos (third from left) attend the opening ceremony of Khashoggi's monument. (Arif Hudaverdi Yaman/Anadolu Agency via Getty Images)
"These apps have become like gates to bad actors," he said, adding there is "a big public market for cyber-offensive vulnerabilities weapons. There are big offensive companies all over the world paying money for these kinds of vulnerabilities."
The bad actors in this situation gained access to Bezos' phone using a method called "phishing." Phishing is a popular hacking technique that tricks people into opening links and sharing personal information to give hackers access to devices.
BEZOS RETAINS CROWN AS WORLD'S RICHEST IN 2019, DESPITE LOSING $38B IN DIVORCE
Sixty percent of Americans say they or a close family member has been a victim or a phishing attack, according to a 2019 report from phishing protection company Retruster. Additionally, there was a 200 percent increase in phishing attacks via social media in 2018, according to Phishlabs.
"Consumers need to recognize that the very value proposition that makes WhatsApp appealing -- privacy and secrecy of messaging -- is what makes it an extremely desirable target for the bad guys and people with bad intentions," Richard Bird, chief customer information officer at software company Ping Identity, told FOX Business. "Secrets are too valuable of an asset for the bad actors not to at least try."
So, if the founder of Amazon can fall victim to phone hacking through social media, how can regular people prevent bad actors from getting access to their phones and personal information? Here are some tips.
Keep your apps up to date
"The first thing is always to make sure your apps are up to date," Vanunu said. "Vendors are always issuing updates. With updates, there are also security backs. It’s very important."
WHAT TYPES OF COMPANIES COULD BE TARGETTED BY AN IRANIAN CYBER ATTACK?
Phone, computer and tablet systems should also be updated on a regular basis.
Be wary of potential phishing messages
If Bezos' hacking story has taught the public anything, it's that people should be cautious when they are opening emails and messages -- especially on social media apps -- that contain links, videos and other content that requires the user to click or open a new tab on a device.
Users should also pay attention to email and general message senders and ask themselves if certain names and addresses are familiar or unrecognizable.
"You can’t tell people not to open videos and messages that are part of the application," Vanunu said. "But they should bear in mind that when they get messages from people they don’t know or groups they don’t trust, they should think twice."
Bird explained that even on an encrypted device or app, bad actors can still get access to sensitive information.
"Secrets are very hard to keep," he said. "Either someone wants them and hunts for them or we slip personally and disclose them. Even with encryption, a secret is still too tempting of a target to someone. WhatsApp is a good encrypted chat platform, but it doesn't change a single thing about the human desire to discover a secret."
Watch out for suspicious-looking calls and texts
Robocalls and scam text messages have unfortunately become the new norm in recent years. Most of these calls and texts are used to scam people into giving out personal information.
Do not pick up phone calls from unrecognizable numbers that look oddly familiar to your own phone number or come from the same area code. Voicemail is always an option for callers who are not scammers. Do not reply to or click on links in text messages that say anything about being the victim of a hacking attempt or being some kind of lucky winner.
Clear your cache
This is a phrase you may hear at work. "Clearing your cache" means regularly deleting browsing history, cookies and other information a device has been trained to immediately recognize when a user opens a particular app or website. This will minimize a user's "virtual footprint," or the amount of data visible to potential hackers.
Download a security app
There are phone security apps for Android and Apple smartphones that many people are unaware of, according to Vanunu.
GET FOX BUSINESS ON THE GO BY CLICKING HERE
"Today on the market, there are some security products you can use that very few people know about and use," he said.
It is crucial, however, that users do their research before downloading and signing up for an app since apps themselves can have vulnerabilities that give bad actors access to personal information.

A Whatsapp App logo behind a Samsung Galaxy S4 phone that is logged on to Facebook in the central Bosnian town of Zenica, Feb. 20, 2014. (REUTERS/Dado Ruvic)
"Consumers need to ask themselves an important question for every app that they use," Bird said. "'Do I trust the solution more than I trust myself when it comes to my safety?' Don't assume the standard security settings in an app as 'safe'; if automatic downloads had been disabled in this case, it appears that this hack could have been avoided."
Understand the threat
Sometimes there is nothing that will stop a bad actor from accessing sensitive information on a device or through an app.
"There is a big public market for cyber-offensive vulnerabilities weapons. There are big offensive companies all over the world paying [millions] for these kinds of vulnerabilities," Vanunu explained.
"The reality of it is that these kinds of vulnerabilities that target Whatsapp and other apps are sophisticated. It’s not fair to say you can prevent these. Usually, it’s very hard to prevent it. They are seamless. This is why they are worth a lot of money in the market," he said.