Coronavirus-themed malware is spreading. Here's how to avoid it
Legitimate-looking map contained malware that had the capabilities to steal victims' sensitive information
Coronavirus-themed malware is becoming more common and more advanced.
Shai Alfasi, a researcher at cybersecurity research firm Reason Labs, released results from a study last week that looked at a specific type of malware that "weaponized" a legitimate coronavirus map application created by Johns Hopkins Health.
The real map tracks where COVID-19 has spread and how many cases have been reported across the globe, but the malware-infested map downloads viruses onto victims' devices.
"The original map came from Johns Hopkins," Alfasi told FOX Business. "All the attacker did was say: We know everyone wants to see this map and be updated" and took advantage of that knowledge to scam users into sharing sensitive information.
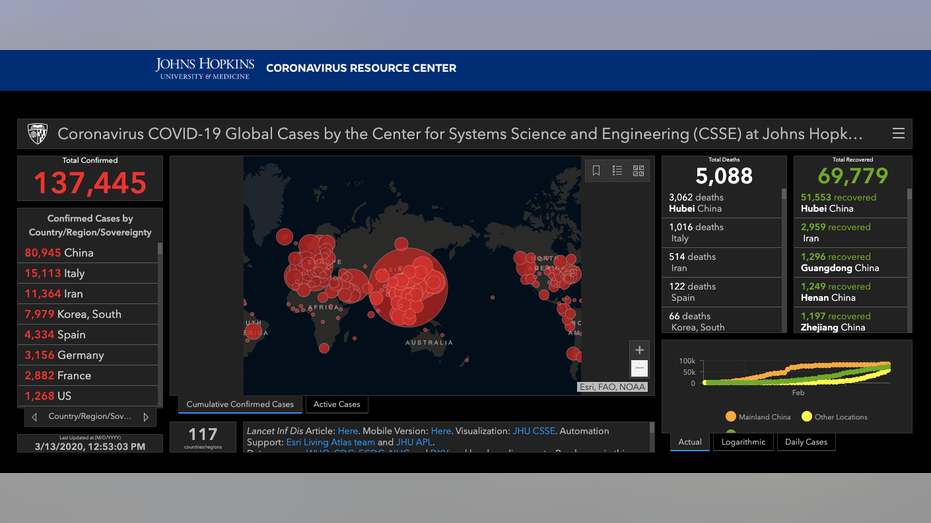
Johns Hopkins coronavirus map/ Johns Hopkins Health
Hackers gathered information from that original map and inserted it into a downloadable file that was malicious. Reason Labs caught the attack before it spread on a larger scale to potential victims, but if people were to come across the malicious map, it would have been in a phishing email or other kind of social campaign, Alfasi explained.
AS CORONAVIRUS SCAMS SPREAD, HERE'S HOW TO PROTECT YOURSELF
"In the background [of the downloadable map] were many other processes that run at the same time to steal a bunch of information that you saved on your browser," he said.
Alfasi concluded that the malware had the capabilities to steal victims' passwords, credit card information, usernames and other sensitive information, according to a March 9 Reason threat analysis report. All a victim had to do was double-click the map to expose themselves to the information-stealing virus.
GET FOX BUSINESS ON THE GO BY CLICKING HERE
But the map isn't the only type of coronavirus-related malware being spread to users across the globe. Reason also discovered phishing emails disguised as official World Health Organization (WHO) notices.
Another cybersecurity research company, Check Point Research, discovered malicious emails from what appeared to be "a long-running Chinese-based operation" that were designed to look as if they were from the Mongolian Ministry of Foreign Affairs, according to a March 12 blog post.
The official-looking emails warned readers about the spread of COVID-19 and malicious downloadable files.
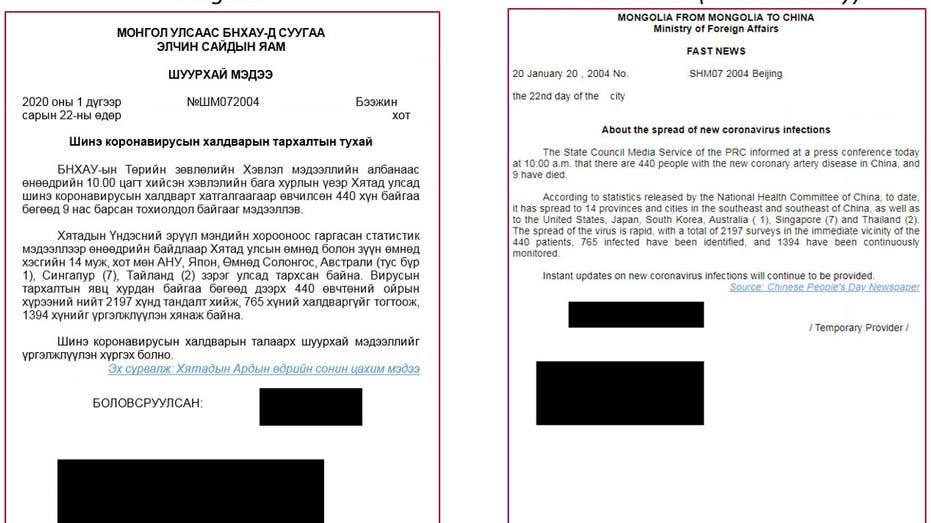
Document 1: Information about the prevalence of new Coronavirus infections/ Check Point Research
"This specific campaign leverages the COVID-19 pandemic to lure victims to trigger the infection chain," CPR concluded.
Additionally, state-sponsored hackers from China, Russia and North Korea have also been discovered deploying COVID-19-themed cybercrime attacks, ZDNet reported last week.
Chinese cybersecurity firm QiAnXin Technology discovered phishing emails disguised as official notices from the World Health Organization and the Center for Public Health of the Ministry of Health of Ukraine.
One such fraudulent email went viral, spreading misinformation about the virus and creating mass chaos in Ukraine, according to a Feb. 20 BuzzFeed report.
The WHO recently sent out a statement regarding these cyberattacks that are disguised as official WHO notices, saying, "Criminals are disguising themselves as WHO to steal money or sensitive information. If you are contacted by a person or organization that appears to be from WHO, verify their authenticity before responding."
The statement added that the WHO will never ask people for usernames or passwords, send unrequested email attachments, ask people to visit a link outside www.who.int, charge money to those who want to apply for a job, ask people to register for conferences or conduct prize-winning lotteries and games via email.
South Korean cyber-security firm IssueMakersLab similarly discovered a North Korean state-sponsored email attack disguised as an official COVID-19 information email that contained malware-infected, downloadable files.
In one last example reported by ZDNet, Vietnamese cyber-security firm VinCSS discovered a phishing email from a Chinese state-sponsored hacking group that appeared to come from the Vietnamese Prime Minister.
Hackers often seize trending online topics like COVID-19 in scam emails, texts and phone calls as a way to get potential victims' attention and install malware on their devices or gain access to sensitive information.
To avoid falling victim to these kinds of realistic-looking scams, Alfasi shared two tips.
"First of all, there is no need to download anything because the map is online," Aflasi said. "Second of all, they need to have some AV [anti-virus] protection, because there is no protection for these kinds of vulnerabilities."
Users should avoid getting any kind of COVID-19 related information via email and instead go directly to the source like the websites for WHO and the Centers for Disease Control and Prevention.
In terms of anti-virus protection, while it is necessary for workplaces to have this in place, one way users can prevent malware from infecting their devices without paying for AV protection is simply by keeping devices and applications up to date. So, next time you get a notification on your phone or computer that says, "Your device is ready for an [X] update," make sure to allow the update to happen rather than dismiss the notification.
Additionally, Alfasi said being aware that these kinds of fraudulent graphics and emails exist in the first place is "the key to solving this issue." If users are aware that their information is at stake by clicking on something that does not come from a trusted source, they can easily avoid falling victim to malware.
Victims of cyberattacks and phishing emails can report their experiences to the FBI, the Cybersecurity and Infrastructure Security Agency and the Federal Trade Commission, as well as their own email providers like Google and Microsoft.




















