Experts say iPhones are easy to unlock, so why is the FBI demanding Apple's help?
'You can't have a back door that's only for the good guys'
The FBI could easily unlock Apple's iPhones with third-party help, experts say, but the government wants more authority over the tech company's products and practices.
Apple and the FBI have gone head to head in recent weeks since the government asked the tech giant to unlock two iPhones used by the 21-year-old member of the Royal Saudi Air Force who shot up a Pensacola, Florida, naval base on Dec. 6, killing three U.S. sailors and injuring eight others.
U.S. Attorney General William Barr said in a Monday statement that Apple has not provided "any substantive assistance" to the U.S. government after it ordered the tech giant to unlock two iPhones -- one model 5 and one model 7 -- used by Pensacola shooter Mohammed Alshamrani.
| Ticker | Security | Last | Change | Change % |
|---|---|---|---|---|
| AAPL | APPLE INC. | 293.32 | +5.88 | +2.05% |
But the iPhone 5 and 7 should not be difficult to unlock, Andrew Garrett, CEO of the computer forensic firm Garrett Discovery, told FOX Business. The technology to do so is readily available, but "the FBI wants an easy button," Garrett said.
Barr added in his statement that it is "critical" investigators be given "access to digital evidence once they have obtained a court order based on probable cause."

Attorney General William Barr. (AP Photo/J. Scott Applewhite)
Apple responded to the accusation in a Monday statement saying it rejects "the characterization that Apple has not provided substantive assistance in the Pensacola investigation. Our responses to their many requests since the attack have been timely, thorough and are ongoing."
APPLE ROBOT WILL EXTRACT VALUABLE MINERALS FROM RECYCLED IPHONES
"Within hours of the FBI's first request on December 6, we produced a wide variety of information associated with the investigation. From December 7 through [Dec. 14], we received six additional legal requests and in response provided information including iCloud backups, account information and transactional data for multiple accounts. We responded to each request promptly," the statement read.
President Trump tweeted on Tuesday that Apple "refuse[s] to unlock phones used by killers, drug dealers and other violent criminal elements."
The FBI could reach out to various services provided to government and law enforcement like Graykey and Cellebrite to crack the iPhones in question in a matter of 60 days, Garrett said.
"Either the powers are misinformed or impatient," he said.
Instead of using numerous accessible resources that could be used to unlock these iPhones, the government is putting the blame on Apple because they want a back door to Apple's encryption technology, Garrett explained.
With backdoor access, the government could continue to access data on locked iPhones without having to contact third-party help and pay large fees.
POPULAR CHAT APP ACCUSED OF BEING SECRET SPY FOR UAE
"It would be a lot easier for [the government] if they had a tool directly from the manufacturer rather than spend a lot of money on hiring a company or buying a tool to do this," Patrick Eller, CEO of digital forensics solutions provider Metadata Forensics, LLC, said.
To prove how easy the process would be for the FBI to gain access to Alshamrani's iPhones, Garrett sent an email to Cellebrite -- a company that unlocks encrypted iPhones -- to see if they would perform his request to unlock an iPhone 8, which is a model more advanced than the latest model used by Alshamrani, for $5,000.
"[I] Have an iphone8 or 7," Garrett wrote to an employee at Cellebrite. "I will have to check when in the office that needs unlocked. Will obtain a court order asap. Device has one last guess to it. Can you do it for the same 5k?"
Cellebrite replied that it "absolutely can."
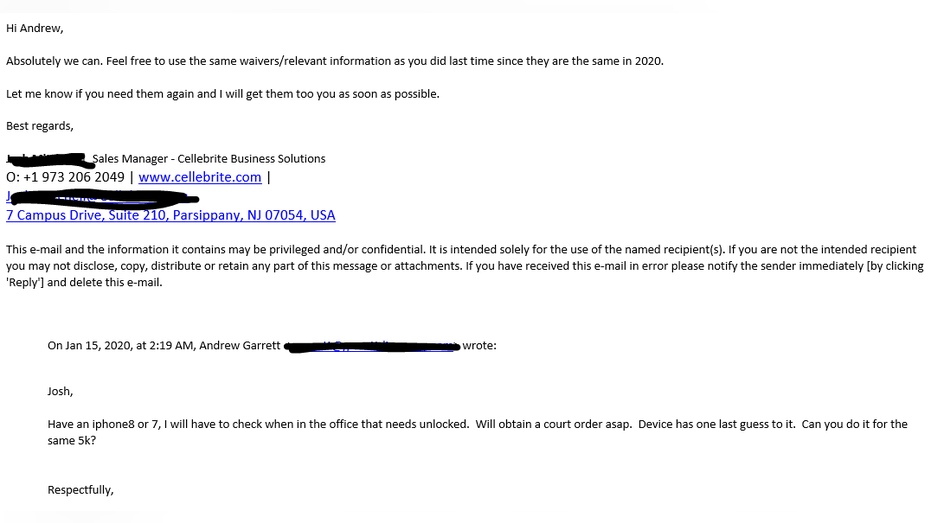
Email exchange with Cellebrite / Andrew Garrett
Garrett said that even though the FBI wants an "easy button," Apple can't provide an easy button because customers wanted strong encryption, or privacy. Apple provides products with strong encryption since it does not trust the U.S. government. If people trusted the government, he said, this would not be an issue.
Additionally, both Garrett and Eller brought up a new encryption breaking tool called "Checkm8" released just yesterday that allows anyone to jailbreak an iPhone -- a tool the FBI could easily get access to. But again, the government would rather have its own backdoor technology into Apple's products to give law enforcement an advantage.
Doing so, however, would also pose a national security risk, experts say.
GET FOX BUSINESS ON THE GO BY CLICKING HERE
"The government’s demand [of Apple] is dangerous and unconstitutional and would weaken the security of millions of iPhones," ACLU Surveillance and Cybersecurity Counsel Jennifer Granick said in a statement.
"Strong encryption enables religious minorities facing genocide, like the Uyghurs in China and journalists investigating powerful drug cartels in Mexico to communicate safely with each other, knowledgeable sources and the outside world," Granick said.
"There is simply no way for Apple, or any other company, to provide the FBI access to encrypted communications without also providing it to authoritarian foreign governments and weakening our defenses against criminals and hackers," she added.

Apple CEO Tim Cook, right, takes a photo with an Apple employee during the launch and sale of the new iPhone 6 at an Apple store in Palo Alto, Calif. (AP Photo/Tony Avelar, File)
Eller agreed with the statement.
"I believe what they’re stating is: If they provide an exploit into those devices, that exploit could be used by other people that are not the law enforcement or government," Eller said.
If Apple gave the government backdoor access to its devices, that knowledge would likely be exposed to bad actors all over the world.
"Someone in Apple is going [would be] paid off by the government to leak it out. That is a guarantee," Garrett said. "Or the FBI is going to come to them, muscle up the person that [can give backdoor access], get the code, share all the information, and before you know it, it will be sold to every dictator around the world."
In the words of Apple CEO Tim Cook himself: "You can't have a back door that's only for the good guys."
READ MORE ON FOX BUSINESS BY CLICKING HERE
And the Pensacola shooting is not an isolated incident. After 14 people were killed and 22 were injured in the 2015 San Bernadino, California, terrorist attack, Apple rejected orders by the U.S. government to unlock iPhones used in the incident and extract data from them that would have been used as forensic evidence.
The government insisted for months that it could not access the iPhone until, at the 11th hour just before a congressional hearing with Apple, the FBI suddenly unlocked the phone and the case was dropped.
The Pensacola shooting investigation "was an opportunity for the FBI to reapproach the same subject as before," Eller said.




















