Russia's alleged hack of US government: Here's what you need to know
Microsoft claims it identified 40 agencies, organizations and companies infiltrated by the hack
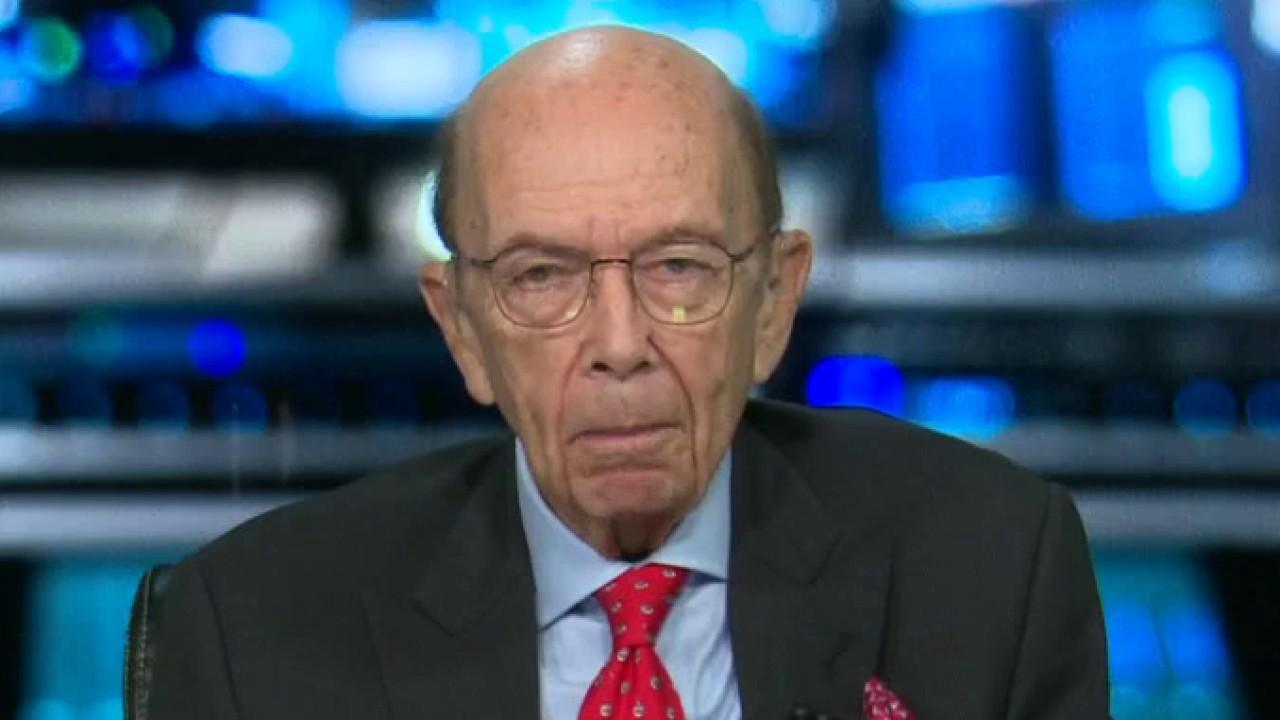
Commerce Secretary Ross: We're taking the cyber hack 'very seriously'
Commerce Secretary Wilbur Ross says there will be more revelations 'soon' regarding the cyber hack backed by a foreign government on the U.S. Treasury Department and an agency within the Commerce Department.
Agencies and businesses across the globe are still trying to make sense of the SolarWinds hack that may have been perpetrated by Russian agents.
A U.S. official, speaking on condition of anonymity, said the hack was severe and extremely damaging, though no agency has been publicly blamed yet. While the full extent of the attack is unknown, the official labeled it "the worst hacking case in the history of America."
"They got into everything," the official added.
Here's what you need to know.
Timeline of events
The Cybersecurity and Infrastructure Security Agency (CISA) on Sunday issued its fifth-ever emergency directive, which mandated government users disconnect from SolarWinds.
REP. STEWART: CYBERSECURITY BREACHES SHOULD 'FRIGHTEN ALL AMERICANS'
SolarWinds services some 300,000 clients, including government agencies and almost all Fortune 500 companies.
| Ticker | Security | Last | Change | Change % |
|---|---|---|---|---|
| SWI | NO DATA AVAILABLE | - | - | - |
Reuters first reported on the attack on Sunday, calling the hackers "highly sophisticated." The report claimed that the National Security Council convened at the White House on Dec. 12 ahead of issuing the emergency directive.
On Sunday, SolarWinds first notified some 33,000 of its customers that an "outside nation state" had found a back door into some updated versions of Orion.

FILE - The U.S. Treasury Department building viewed from the Washington Monument in Washington. Hackers got into computers at the U.S. Treasury Department and possibly other federal agencies. (AP Photo/file)
SolarWinds admitted that there was a "potential vulnerability" related to its updates between March and June for software products called Orion.
"In a nutshell, SolarWinds' Orion product provides centralized monitoring across an organization's entire IT stack. That means the attackers who were able to compromise this platform had an extremely high level of access to all of these client systems," David Kennedy, CEO of TrustedSec, told Fox News.
Later on Sunday, Dec. 13, the White House confirmed the reports, saying that the government was "taking all necessary steps to identify and remedy any possible issues related to this situation."
The attack is also suspected to be connected to a breach at U.S. cybersecurity firm FireEye, which said that its investigation into the hack identified a "global campaign" that targeted governments and businesses by inserting malware into SolarWinds updates beginning last spring.
| Ticker | Security | Last | Change | Change % |
|---|---|---|---|---|
| FEYE | NO DATA AVAILABLE | - | - | - |
White House Deputy Press Secretary Brian Morgenstern said Friday that President Trump has made it clear that the federal government is working with interagency groups and response teams; the FBI, DHS, ODNI and NSA.
"Ambassador Robert O'Brien is convening meetings more than once a day to work with agencies to mitigate effects," Morgenstern added. "We will not forecast any response to adversaries."

FILE - This Tuesday, Aug. 4, 2009, file photo shows the U.S. Chamber of Commerce building in Washington. Elite cyberspies have spent months secretly exploiting SolarWinds software to peer into computer networks. (AP Photo/File)
Who was involved?
FireEye said it confirmed intrusions in North America, Europe, Asia and the Middle East.
The Washington Post then reported that the FBI is investigating whether a group connected to the Russian Foreign Intelligence Service, SVR, is behind the attacks. Suspected hackers are known by the nicknames APT29 or Cozy Bear.
However, Kremlin spokesman Dmitry Peskov denied Russia was involved.
"Once again, I can reject these accusations," Peskov told reporters. "If for many months the Americans couldn’t do anything about it, then, probably, one shouldn’t unfoundedly blame the Russians for everything."
What agencies were affected?
As it stands now, the U.S. State Department, Department of Homeland Security (DHS), and elements of the Department of Defense have reported being compromised. The hack may have lasted for months, targeting Treasury and Commerce departments.
Government agencies, such as the Department of Energy, moved quickly to protect themselves and investigate the incidents.
WHAT IS SOLARWINDS? A LOOK AT THE HACKED SOFTWARE COMPANY IN CROSSHAIRS
"At this point, the investigation has found that the malware has been isolated to business networks only, and has not impacted the mission-essential national security functions of the Department, including the National Nuclear Security Administration (NNSA)," DOE Spokeswoman Shaylyn Hynes told Fox News.
"When DOE identified vulnerable software, immediate action was taken to mitigate the risk, and all software identified as being vulnerable to this attack was disconnected from the DOE network."
Microsoft's response
Tech giant Microsoft revealed on Thursday that it had identified more than 40 government agencies, think tanks, non-governmental organizations and IT companies infiltrated by the hackers – four in five of which were in the United States, nearly half of them tech companies.
| Ticker | Security | Last | Change | Change % |
|---|---|---|---|---|
| MSFT | MICROSOFT CORP. | 415.12 | -5.65 | -1.34% |
"This is not ‘espionage as usual,’ even in the digital age. Instead, it represents an act of recklessness that created a serious technological vulnerability for the United States and the world," Microsoft said in a blog post.
CLICK HERE TO GET THE FOX NEWS APP
"While the most recent attack appears to reflect a particular focus on the United States and many other democracies, it also provides a powerful reminder that people in virtually every country are at risk and need protection irrespective of the governments they live under."
Fox News’ Audrey Conklin, Hollie McKay and Chris Ciaccia contributed to this report, as well as The Associated Press.