After NSA Leaks, Should Businesses Reconsider Contractors?
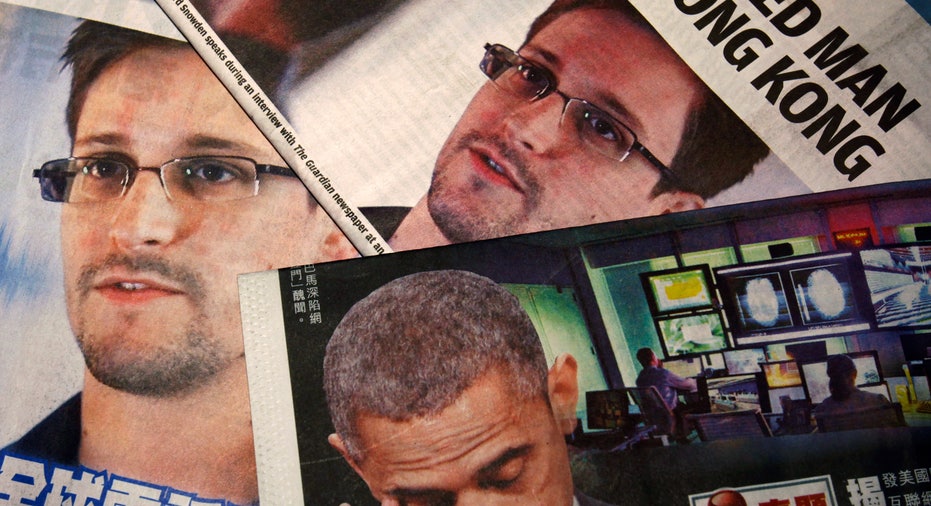
For many small businesses, contractors are often the best solution for short-term assignments or for projects outside of a company’s expertise. But as ex-NSA contractor Edward Snowden revealed himself to be the source behind the agency’s grand-scale security leaks, it raises the question: should businesses trust contractors with sensitive data?
The consulting firm Booz Allen Hamilton fired the former CIA employee this week after news of the breach, and while some consider Snowden to be a hero and others a traitor, from a business perspective, the idea of a contractor releasing sensitive data to the public is a business owner’s nightmare.
“There’s always the worst-case scenario, which is exactly what the NSA is dealing with right now. It’s an extremely trusted vendor, and they’ve gone through all the checks and balances,” says Dave Aitel, the CEO of high-tech security firm Immunity and a former NSA computer scientist.
Aitel says for most companies, however, little tweaks can go a long way to making sure they never have to experience a worst-case scenario, like having private data or trade secrets stolen and/or leaked by a contractor.
“Small changes in behavior, and investing a little bit in technology – you have to do both,” says Aitel.
Managing the Risks of Using Contractors Aitel says many businesses are moving away from offshoring jobs and projects, once they realize the risks and additional security costs.
“They’re looking at the price advantages of offshoring … the productivity often isn’t there, and the security and technology costs necessary so they’re not taking on crazy risks … make it not worth it,” he says. “But it’s sometimes the only way to get the job done,” he admits, pointing out that nobody does their own plumbing – unless they run a plumbing business.
When it comes to outsourcing safely and effectively, Aitel suggests business owners keep their eyes open to internal security risks – rather than just protecting themselves against external threats like hackers.
“The obvious solution is much greater internal monitoring – and having someone who manages and utilizes that data,” says Aitel.
He says many businesses with sensitive data are “crunchy on the outside and chewy on the inside.” As soon as someone gains access through the proper channels – like Snowden within the CIA – companies without active internal monitoring are at great risk.
Aitel’s first suggestion is to make a list of every program that employees use or have access to. Once business owners understand their baseline operations, they can quickly investigate if something suspicious or irregular is occurring.
Don’t Leave Home With Your Secrets Aitel says businesses in the intelligence, government or military communities face greater threats to security, as do those in energy production or manufacturing.
When travel is required to countries that pose an “active threat,” like China, Aitel suggests employees travel with a burner computer – one that doesn’t have any sensitive data stored on it and can’t connect back to the company’s headquarters.
“Otherwise, you can assume the Chinese have everything,” says Aitel, calling it a “very realistic threat.”
Another smart and simple solution is to encrypt important e-mails, such as those containing legal information or sensitive data. He recommends the downloadable software Pretty Good Privacy for encryption, or the technology available through Microsoft Outlook.
Legal Safeguards for Working with Contractors In addition to IT precautions, RocketLawyer CEO Charley Moore says businesses also need to take legal steps to protect themselves when working with contractors.
“First, every independent contractor should enter into a confidentiality agreement with the company,” says Moore.
Work-for-hire clauses also need to be put down in writing in contractor agreements. This means that any work done by the contractor is owned by the company and not the individual – so they can’t run away with it and sell it to a competitor, for instance.
Moore also suggests an “invention assignment” clause, which ensures any inventions developed while working with the business become property of the company.
“It’s important that you give the contractor an opportunity to list separate inventions he’s already created,” says Moore, so there’s no confusion around which inventions belong to the contractor, and which belong to the company.
In terms of what qualifies as an “invention,” Moore says anything that can be patented, trademarked or copyrighted counts. “An app, software or anything considered intellectual property” should also be included,” he adds.
And Moore says what’s more important than what you tell your independent contractors is knowing what you shouldn’t.
“Only provide information to a contractor on a need-to-know basis,” he says.



















